
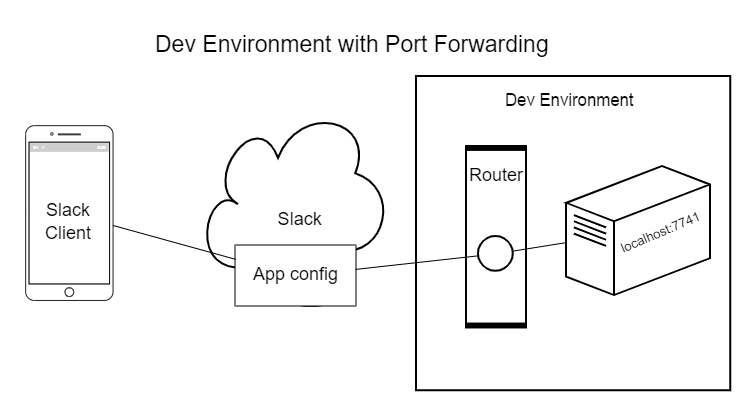
When you have a local resource (e.g., http://localhost:8080) that you need to access from the internet for debugging purposes, you have a few common options. You could open a port in your firewall and forward the request to your resource if you have control over your network, you could create a VPN, or you can run a utility on your machine that creates a tunnel from the internet to your resource bypassing your firewall. That’s where Cloudflare comes in.
In this post, I’ll show you how to use the new, web-based interface in Cloudflare to quickly configure a tunnel to your local resources for free. I’ll share some resources to improve the security and resiliency of the tunnel if you need it on a more permanent basis as well.
If you want to follow along, you will need to own a domain and have Cloudflare manage its DNS. Cloudflare DNS is free, fast, and provides some nice tools like full SSL, analytics, and filtering out traffic by country.
Without further ado, let’s get started.
Real-World Example
Working at Keyhole Software is fun and challenging. I’m always looking at ways to stay on top of new technologies and generally keep my wits smart, so a few years ago, I created a Slack app called Picker.
Picker solves the problem of who is going to complete my code review for me by randomly choosing one (or more) team members from my Slack channel to complete the request. Picker grew into a lot more than that with the help of my friend and co-worker Adam. Now, it helps teams do things like automatically picking who leads the stand-up meeting every day at 9 am.
Instead of opening a port on my router that any port scanner can find and abuse, I had been using a little tunnel console utility on my computer called ngrok. Every time I would want to debug something, I would need to run ngrok, navigate to where my configuration lives in Slack, and update three different spots with the ephemeral URL that ngrok assigned me. It is possible to pay ngrok for a permanent address, but it wasn’t worth the money for my purposes.
Cloudflare Tunnel
Cloudflare recently announced they added a simple GUI to their Zero Trust offerings for creating tunnels easily compared to the former CLI version that required several steps and key management. It took me just 5 minutes to configure my first tunnel!
Cloudflare has great step-by-step instructions to follow, but the gist is…
- Log in to Cloudflare and navigate to the Zero Trust dashboard from the left menu.
- Expand Access in the left menu, and then navigate to Tunnels.
- Create a new tunnel with the idea being you will have one tunnel configuration per machine.
- Download the small service to the machine you will be using for debugging.
- Execute a command on your machine to link that service to your Cloudflare tunnel configuration.
- Next, you can choose to connect an application or a network.
- For my purposes, I chose an application and selected a domain that Cloudflare already managed and then set the application to be http://localhost:7041.
- Save & Done! Your tunnel is now connected.
I am using a Windows 11 PC, and the service Cloudflare installed is configured to start automatically each time my computer reboots. After my tunnel was in place, I went to Slack and configured the three different settings I have to use the new Cloudflare-based URL. With that, I said goodbye to always having to update those.
Taking it Further
Cloudflare DNS
To use Cloudflare Tunnel, your domain DNS needs to be managed in Cloudflare. That worked well for me because I was already a fan of their offerings and have several domains set up. Of the many benefits I like about Cloudflare DNS, two include the remote proxy and the automatic SSL.
The reverse proxy gives my static home IP address a layer of security through obscurity. Anyone scanning my domain will only see as far as the Cloudflare IP address. They will never get to know what my home IP address is. I’m sure my home IP address still gets randomly scanned, but at least I can assume it will be slightly safer by obscuring it this way.
The automatic SSL is great for hobby projects. If you purchase a domain and configure the DNS to be managed by Cloudflare, you can apply end-to-end HTTPS with various versions of TLS configurable for free.
There are a lot more bells and whistles with Cloudflare DNS. One other worth mentioning is the ability to create geospatial firewalls so that you can limit what countries can access your domain. It’s just one more layer of security through obscurity you can use to help protect yourself.
You may be aware that Cloudflare also provides its upstream DNS service with 1.1.1.1 to provide a fast, privacy-focused DNS resolver. But did you know they added new addresses for blocking malware (1.1.1.2) and malware & adult content (1.1.1.3)?
And, if you are using your device on public wifi, you can install their dead-simple VPN service to help protect your traffic – check out WARP.
Cloudflare Identity
You can further limit who can access your resources by using Cloudflare’s Zero Trust integration with SSO, user management, service auth, or even a turn-key login page.
Cloudflare Tutorials
Check out this list of tutorials to give you some ideas for things to try out on your own. Render an SSH or VNC client in a browser and connecting over RDP all look interesting.
Wrap Up
I started using Cloudflare as an easy way to manage my DNS and get SSL, then slowly have been exploring their other offerings. I’m really excited about the new tunnel I set up. I hope you have been inspired to try setting one up, too, or have seen other offerings that could make your projects more secure or easier to manage. I know I’ll be working on taking the tunnel I configured and trying to make it even more secure by adding in some authentication.
Drop a comment below to let me know if you try out any of these, and tell me how it goes for you! If you enjoyed this post, make sure you check out the rest of the Keyhole Dev Blog for more.
More From Rusty Divine
About Keyhole Software
Expert team of software developer consultants solving complex software challenges for U.S. clients.



If you are running Home Assistant, here is a Cloudflared plugin that will let you close your firewall ports: https://osmy.in/3KpqsgN
That Cloudflared plug-in also include nginx proxy manager. This allows you to quickly and easily setup other subdomains through Cloudflare. Once setup you’ll instantly see them in your Cloudflare dashboard as well. It’s pretty slick!
<a href=”https://full-softwares.com/vnc-connect-enterprise/”>VNC Connect Enterprise</a> I am very impressed with your post because this post is very beneficial to me and provides new knowledge to me.
Does it able to get visitor real ip? I don’t think so
What if I want to connect my localhost mysql databsse server to cloudflare tunnel and use it separately and remotely for my other desktop applications?